Situation:
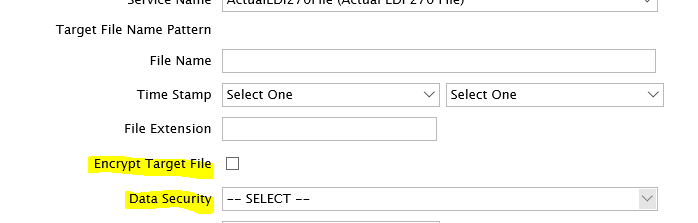
I have been trying to figure out how to setup an FTP target with PGP encryption and am a little stuck...I created the Key Manager and Data Security, but in the FTP Target form, it will only let me select the Key Manager if I check the SSH box and the connection only test successfully when that box isn't checked...so what am I doing wrong?
Tip:
If you'd like to use encryption or decryption without creating a process flow, you can use the existing B2B framework to do so. This would be under the Translation properties section of the relationship.
Comments
0 comments
Article is closed for comments.