The POODLE Attack
POODLE is a serious vulnerability in SSL 3.0 that can be exploited to steal certain confidential information, such as cookies. By exploiting this vulnerability, an attacker can gain access to things like passwords and cookies, enabling him to access a user’s private account data on a website. Any website that supports SSLv3 is vulnerable to POODLE, even if it also supports more recent versions of TLS.
SSL version 3.0 being no longer secure, browsers and websites need to turn off SSLv3 and use more modern security protocols, to avoid compromising users’ private information. Sites that require SSLv3 will remain vulnerable until they exclude the support of SSLv3.
As the attack mentioned above requires an SSLv3 connection to be established, disabling SSL 3.0 protocol in the client or in the server (or both) will completely eliminate it. Following are the steps to disable SSLv3 protocol using Adeptia Suite:
Steps to disable SSLv3 protocol in Jetty:
1. Go to /ServerKernel/etc/jetty folder and open the Jetty.xml file.
2. Update the sslContextFactory definition section of Jetty.xml file as highlighted in the following figure.
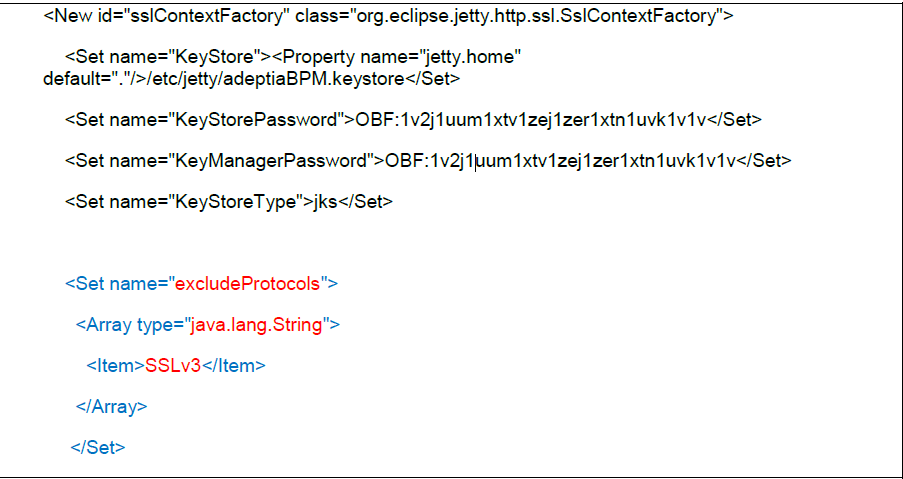
You can copy the text below
<Set name="excludeProtocols">
<Array type="java.lang.String">
<Item>SSLv3</Item>
</Array>
</Set>
Note: In case there are multiple sslContextFactory definitions in the Jetty.xml file, then you need to update each one.
3. Save the file and restart the Kernel and WebRunner.
Comments
0 comments
Article is closed for comments.